Cybersecurity Alert: New Zero-Day Exploit Targets IoT Devices
Cybersecurity Alert: New Zero-Day Exploit Targets IoT Devices, detailing technical specs, market trends, and 2026 predictions.

Cybersecurity Alert: New Zero-Day Exploit Targets IoT Devices
In a significant escalation of the 2026 digital threat landscape, cybersecurity researchers have identified a critical Zero-Day exploit targeting the core firmware of millions of Internet of Things (IoT) devices. This vulnerability—codenamed "ShadowNode"—circumvents traditional network defenses by exploiting a flaw in the universal Plug-and-Play (uPnP) protocol, allowing attackers to gain full administrative control over smart home hubs, industrial sensors, and medical devices.
Technical Breakdown of ShadowNode
The exploit targets a memory corruption vulnerability within the communication stack used by various IoT chipsets. Unlike typical malware, ShadowNode does not require user interaction; it scans for exposed ports and executes a remote code injection that bypasses the device’s secure boot.
-
Remote Code Execution (RCE): Attackers can execute arbitrary commands at the system level, turning the device into a "zombie" node within a larger botnet.
-
Lateral Movement: Once a single device—such as a smart lightbulb—is compromised, the exploit can jump across the local network to target more sensitive hardware, including laptops and storage servers.
-
Firmware Persistence: The exploit modifies the bootloader, meaning a factory reset is often insufficient to remove the infection.
Impact on the 2026 Tech Ecosystem
This alert comes at a time when India’s 2026 tech spending is increasingly directed toward smart infrastructure and industrial automation.
-
Industrial Risks: In manufacturing hubs where IoT-driven automation is standard, a compromise could lead to physical production shutdowns or equipment damage.
-
Privacy Concerns: With the rise of deepfake and AI-driven threats, compromised IoT cameras and microphones provide high-quality "source material" for AI-generated impersonation scams.
-
Data Exfiltration: The exploit is capable of intercepting data packets before they are encrypted, posing a severe risk to businesses managing sensitive client information.
Threat Mitigation Matrix
| Defense Layer | Recommended Action | Implementation Level |
| Network | Disable uPnP on all routers immediately. | Router Firmware |
| Isolation | Move IoT devices to a separate VLAN (Virtual Local Area Network). | Network Admin |
| Hardware | Ensure devices utilize the latest chip-level security features. | Device Choice |
| Monitoring | Deploy Multiagent Systems for real-time traffic anomaly detection. | Enterprise Cloud |
The Developer’s Responsibility
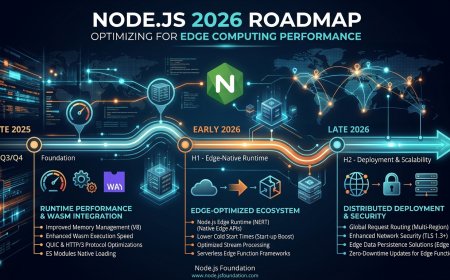
As outlined in the Node.js 2026 Roadmap, security must now be moved to the "Edge". Developers building for IoT must:
-
Implement Zero-Trust architectures where every device request is verified, regardless of its origin within the network.
-
Utilize hardware-backed keystores to ensure that firmware updates are cryptographically signed and cannot be tampered with by exploits like ShadowNode.
Immediate Next Steps for Users
If you own smart home devices or manage industrial IoT hardware, check your manufacturer’s support page for an emergency patch. Until a patch is applied, it is strongly advised to disconnect non-essential IoT devices from the internet to prevent them from becoming a gateway for broader network infiltration.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Wow
0
Wow
0
 Sad
0
Sad
0
 Angry
0
Angry
0













Comments (0)